Network access control (NAC) solutions are network security components that enable IT security teams to verify the authorization and access levels for every device and user. NAC solutions should employ zero-trust and offer real-time monitoring, asset visibility, and compatibility with your existing systems. To help you choose a suitable solution, I’ve analyzed each solution’s differentiating features below, followed by the key NAC functions to consider.
Here are the top six NAC solutions:
- NordLayer NAC: Best overall network access control tool
- Ivanti Policy Secure: Best for core features and compliance
- Portnox Cloud: Best for pricing accessibility and transparency
- FortiNAC: Best choice for advanced protection functions
- Aruba ClearPass: Best for ease of use and administration
- ForeScout: Best option for diverse network environments
Table of Contents
Featured Partners: Network Access Control (NAC) Software
Top Network Access Control Solutions Comparison
This table compares the top six NAC solutions, allowing you to make informed decisions based on affordability and capabilities. It’s based on key factors such as asset profiling, automated guest access, zero-trust architecture, and automated remediation features. It also provides the lowest subscription or licensing cost for each solution.
| Asset Discovery, Visibility & Profiling | Automated Guest Access | Zero Trust Architecture | Automated Remediation | Lowest Tier Cost | |
|---|---|---|---|---|---|
| NordLayer NAC | ✔️ | ➕ | ✔️ | ✔️ | $7/month/user |
| Ivanti Policy Secure | ✔️ | ✔️ | ➕ | ✔️ | Contact sales |
| Portnox Cloud | ✔️ | ✔️ | ✔️ | ✔️ | $200/month/admin |
| FortiNAC | ✔️ | ➕ | ✔️ | ➕ | $92/month/100 endpoints |
| Aruba ClearPass | ➕ | ➕ | ✔️ | ➕ | $710/perpetual license/100 endpoints |
| ForeScout | ✔️ | ❌ | ✔️ | ✔️ | Contact sales |
✔️= Yes ❌= No/Unclear ➕= Limited/Add-On
While other solutions have excelled in specific categories, our analysis indicated that NordLayer offers the best overall value for consumers looking for an effective network access control tool. Continue reading to find out how each choice performed in terms of pricing, features, and key use cases, or jump straight to our product evaluation criteria.
Note: All per-user prices are based on a one-year commitment unless otherwise noted.
NordLayer NAC – Best Overall Network Access Control Tool
Overall Rating: 4.3/5
- Core features: 4.6/5
- Advanced protection functions: 4.5/5
- Pricing and transparency: 4.3/5
- Ease of use and admin: 4/5
- Customer support: 3.5/5
- Security regulations compliance: 4.3/5
NordLayer NAC tops our list among all the solutions, offering a wide set of features for a fully functional NAC tool. It offers asset discovery, visibility, and profiling while maintaining compatibility with current systems, tools, and OS. NordLayer also has strong capabilities in network segmentation, policy management, and automated remediation. With zero-trust architecture and authentication, NordLayer reinforces its position as one of the market leaders in NAC.

Pros
Cons
Ivanti Policy Secure – Best for Core Features & Compliance
Overall Rating: 4.2/5
- Core features: 5/5
- Advanced protection functions: 4/5
- Pricing and transparency: 3.1/5
- Ease of use and admin: 3.5/5
- Customer support: 4.7/5
- Security regulations compliance: 5/5
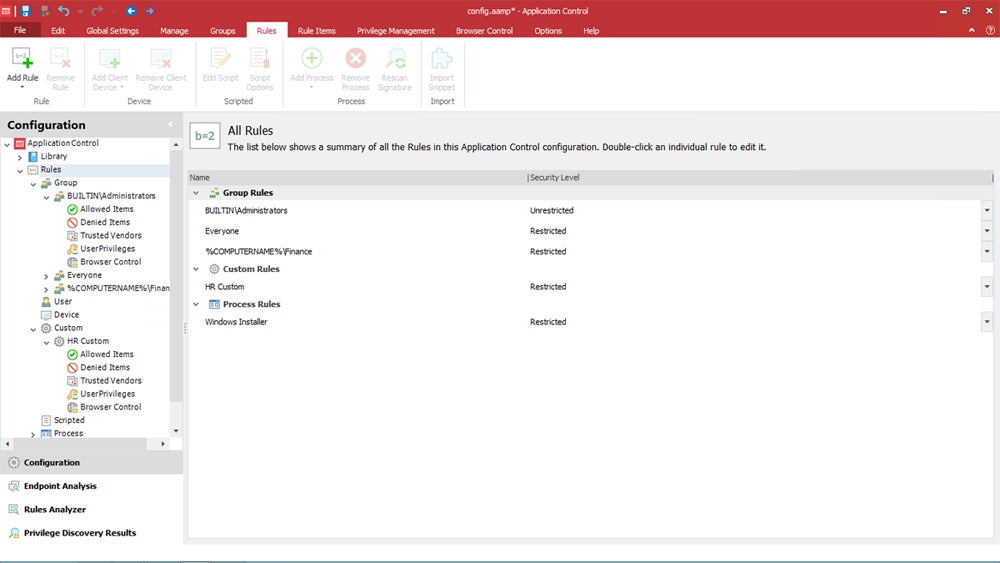
Ivanti Policy Secure offers comprehensive NAC features and adheres to a wide range of compliance standards. The solution encompasses local and remote endpoints to enforce foundational network security policies and control network access for managed and unmanaged endpoints, including IoT. The platform enforces access policies and also integrates with other Ivanti products to provide zero trust network access and user behavioral analytics.

Pros
Cons
For the full list of features, pros, and cons and more details on pricing, explore our complete assessment on Ivanti Policy Secure.
Portnox Cloud – Best for Pricing Accessibility & Transparency
Overall Rating: 4/5
- Core features: 4.8/5
- Advanced protection functions: 4/5
- Pricing and transparency: 4.6/5
- Ease of use and admin: 3.3/5
- Customer support: 2.9/5
- Security regulations compliance: 3.5/5
Portnox Cloud, a cloud-native NAC-as-a-Service solution, provides swift deployment and relieves IT teams of maintenance burdens because of its SaaS model. It stands out for its transparent pricing, free trial and demo information, and full-service installation, making it suitable for SMBs looking for NAC capabilities without a large IT footprint. While smaller businesses benefit from the low total cost of ownership, larger companies can opt for in-house NAC solutions for greater control and customization.

Pros
Cons
For an extensive look at this solution, including its complete feature set, pros, cons, and pricing details, refer to our detailed review of Portnox NAC.
FortiNAC – Best for Advanced Protection Functions
Overall Rating: 4/5
- Core features: 4.4/5
- Advanced protection functions: 5/5
- Pricing and transparency: 3.9/5
- Ease of use and admin: 3/5
- Customer support: 3/5
- Security regulations compliance: 3.5/5
Fortinet’s FortiNAC provides enhanced protection capabilities including endpoint compatibility with IoT, IIoT, and OT devices, consolidating control over complex networks. It caters to smaller companies with solutions for as few as 25 (virtual appliance) or 100 (physical appliance) users, while bigger enterprises benefit from its automated guest onboarding feature and BYOD. The latest FortiNAC version also removed the limitation that prevented network access due to scan failures, hence advancing its overall network accessibility and security.
Pros
Cons
To know more about this solution, see our in-depth FortiNAC product evaluation.
Aruba ClearPass – Best for Ease of Use & Administration
Overall Rating: 3.9/5
- Core features: 4.1/5
- Advanced protection functions: 4.5/5
- Pricing and transparency: 3.9/5
- Ease of use and admin: 4.3/5
- Customer support: 3.5/5
- Security regulations compliance: 2/5
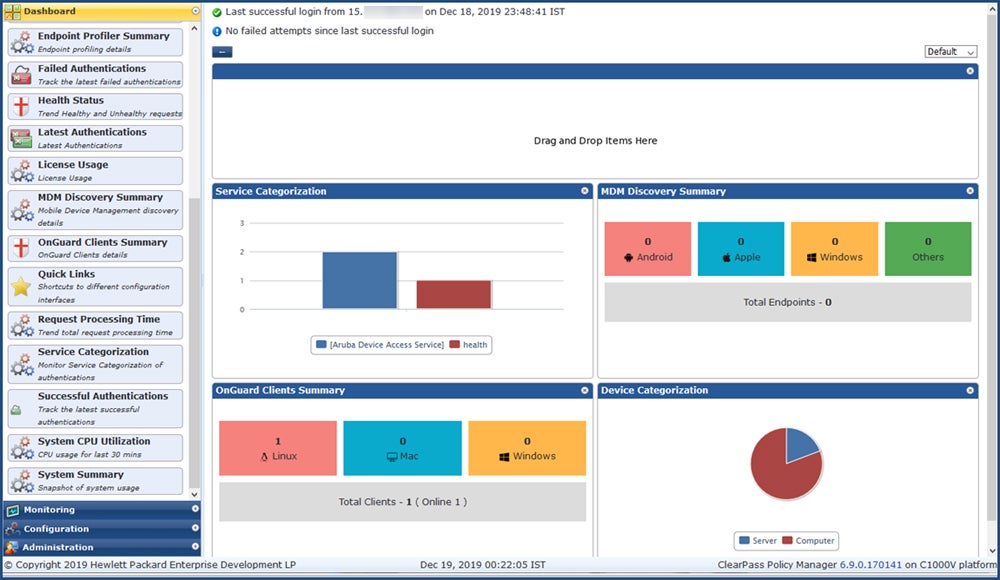
Aruba’s ClearPass suite, which includes Policy Manager, OnGuard, and OnBoard, prioritizes easy administration and operation. ClearPass simplifies network management, especially in high-traffic environments, with features such as clustering for scalability and automated onboarding. The most recent release includes improvements like TLS 1.3 compatibility and a system CLI command for cache management, which streamlines administration tasks.

Pros
Cons
Read our full review of Aruba ClearPass Policy Manager to get a more comprehensive assessment of the solution’s features, pros, cons, and pricing.
ForeScout – Best for Diverse Network Environments
Overall Rating: 3.6/5
- Core features: 4.6/5
- Advanced protection functions: 4.5/5
- Pricing and transparency: 2.4/5
- Ease of use and admin: 4/5
- Customer support: 2.7/5
- Security regulations compliance: 2.8/5
ForeScout Platform, originally known as CounterACT, is a vendor-agnostic NAC solution that provides a non-disruptive installation for smooth integration with network devices and rapid deployment in current environments. It also provides various established third-party integrations. The newer versions include several modules that provide real-time asset inventories, policy-based controls, and security integration while extending NAC controls to the cloud and across sectors.

Pros
Cons
Refer to our full review of the ForeScout Platform for more information on features, benefits, limitations, and cost.
Top 5 Features of NAC Solutions
Network access control solutions can offer many different capabilities and levels of security, including access control and monitoring, automated onboarding, asset discovery, policy management, and third-party integrations.
Access Control & Monitoring
This feature can grant access at the level of granularity needed to satisfy the organization’s security, risk, and compliance requirements to block, quarantine, and grant varying degrees of access.
Automated Guest Access & Onboarding
Automated guest access management and automation should be able to handle the organization’s expected volume and type of guest access. Additionally, automated onboarding of corporate and BYOD devices should be considered to remove the burden of setup and approvals from the IT or Help Desk teams.
Asset Discovery, Visibility & Profiling of Devices
It’s important to monitor, secure, and provide appropriate access to every new endpoint (workstations, laptops, IoT, etc.). Tools should at least be able to discover and manage the majority of the expected endpoint types and volume of users for the network and should automatically block rogue devices.
Policy Management
This feature should provide sufficient capabilities to define and administer security configuration requirements, assign access levels to specific groups, and specify the specific actions for the NAC to take with both compliant and non-compliant endpoints.
Third-Party Security Integration
Integrations with other solutions like security information and event management (SIEM) systems and next-generation firewalls (NGFW) can accelerate security responses, enable more robust responses to threats, and increase the context and utility of alerts. Some NAC tools will even have built-in security functions to provide additional protection.
How I Evaluated the Best NAC Solutions
I assessed the NAC solutions across six main categories, each with particular subcriteria. These factors were weighted based on importance, and each tool received a score out of five depending on each subcriterion’s performance and availability. The final scores determined the top six tools. Then, I evaluated the ideal use case for each solution by taking into account its highest score and conducting additional research on user input and other relevant resources.
Evaluation Criteria
In this evaluation, I prioritized the core features of an NAC solution because of their fundamental function. Advanced protection functions follow, as these are the features solidifying the security of the solution. Pricing and transparency holds the same weight as the advanced features as it determines accessibility and long-term expenses. Then, I assessed the ease of use and admin for improved operational efficiency. Lastly, I examined customer support and compliance.
- Core features (25%): Compares all features necessary for a fully functioning NAC solution including access control and real-time monitoring, device discovery, policy management, and more.
- Criterion winner: Ivanti Policy Secure
- Advanced protection functions (20%): Considers additional security features like third-party security integrations, wired, wi-fi, and vpn access coverage, non-standard device support, and device health insights.
- Criterion winner: Fortinet FortiNAC
- Pricing and transparency (20%): Assesses free trial and demo availability, pricing information accessibility and transparency, pricing models, and the lowest subscription or licensing cost.
- Criterion winner: Portnox Cloud
- Ease of use and admin (15%): Evaluates features such as intuitive user interface, centralized management console, automated onboarding, and user reviews from different platforms.
- Criterion winner: Aruba ClearPass
- Customer support (10%): Includes the availability of live chat, email, and phone support, and user reviews on customer service from platforms like Capterra and Gartner.
- Criterion winner: Ivanti Policy Secure
- Security regulations compliance (10%): Checks the adherence and certifications to major security compliance like ISO 27001/9001, HIPAA, PCI, GDPR, SOC2, NIST, and other specialized compliance standards.
- Criterion winner: Ivanti Policy Secure
Frequently Asked Questions (FAQs)
What Are the Benefits of Network Access Control?
Network access control provides several organizational benefits, including user and application access control, contractor and guest management, role-based access policies, cybersecurity protection, automated incident response, and comprehensive access reports, all of which improve overall network security and management efficiency.
Are There Different Types of NAC?
There are two types of NAC: pre-admission and post-admission. Pre-admission NAC examines access requests based on security policies, which frequently include authentication requirements such as 2FA. Post-admission NAC restricts network movement, preventing cyberattacks by requiring extra authentication.
How Do You Implement Network Access Control?
To implement NAC solutions, first map endpoint devices and create a network access control list. Determine user permissions and set up the necessary technology, such as authentication mechanisms and policy enforcement points. To ensure best security, keep systems up to date on a regular basis.
Bottom Line: Control Your Network Access ASAP
As network connections evolve, so does the likelihood of breaches as attackers exploit weaknesses. NAC solutions provide effective control while responding to varied organizational needs and resources. While regulatory requirements could encourage adoption, user and device control helps all enterprises by reducing risks and costs. Utilize the free trial or demo to see if the solution you prefer matches your needs.
To achieve holistic network security, familiarize yourself with the different types of firewalls so you can create a layered defensive plan that effectively protects your network from numerous threats and vulnerabilities.
Chad Kime contributed to this article.